If you use the internet, you are constantly interacting with cryptographic systems—TLS handshakes, package signatures, SSH keys—whether you notice it or not.
At its core, modern cryptography is built on two primitives:
- Symmetric encryption (shared secret)
- Asymmetric encryption (public/private key pairs)
🧠 Symmetric Encryption
Symmetric cryptography uses a single secret key for both encryption and decryption. This is computationally efficient and forms the backbone of high-throughput encryption systems.
ciphertext → [D_k] → plaintext
⚡ Advantages
- O(n) performance with very low overhead
- hardware acceleration (AES-NI, ARMv8 Crypto Extensions)
- ideal for bulk data (disks, TLS payloads)
⚠️ Core Problem: Key Distribution
🔧 Example
- AES-256 (block cipher, 128-bit block size)
- Modes: GCM (authenticated), CBC (legacy), CTR
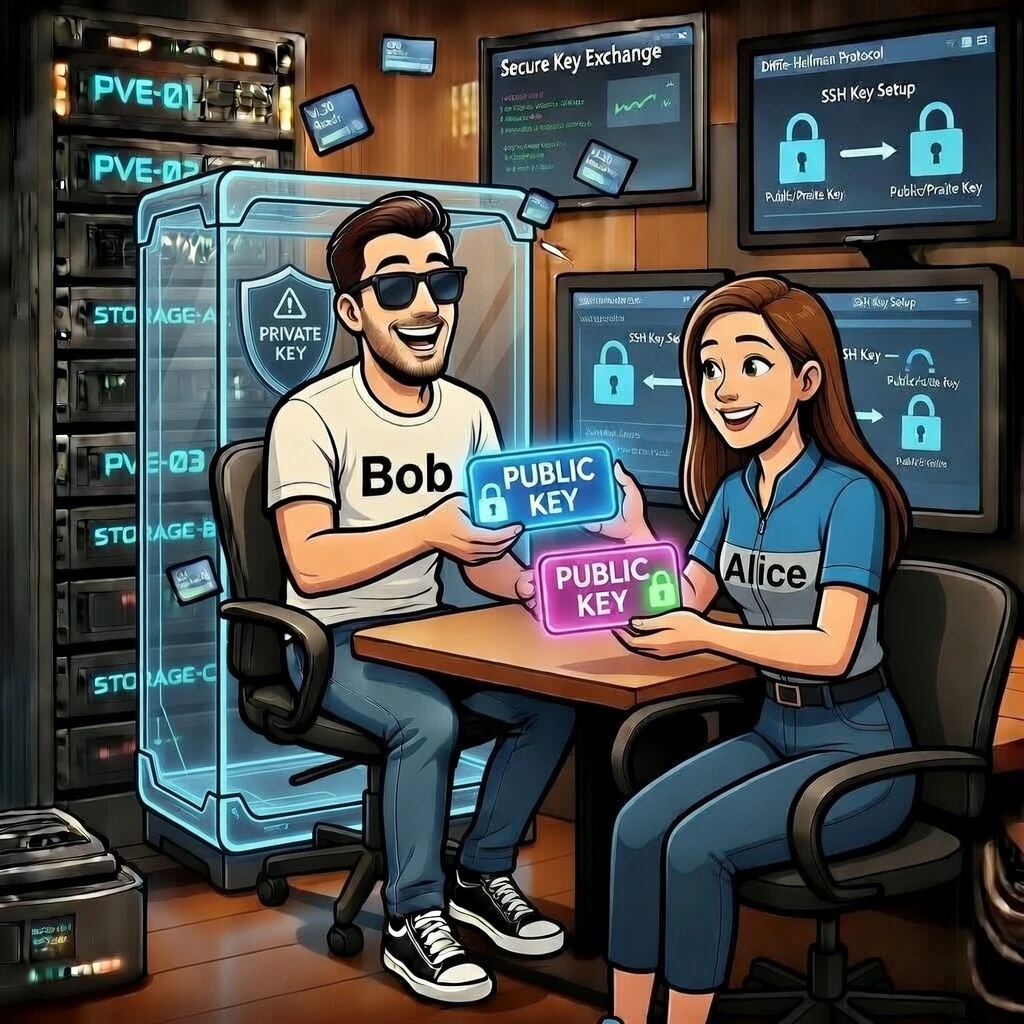
🧬 Asymmetric Encryption
Asymmetric cryptography solves the key distribution problem by splitting identity and secrecy:
- Public Key → can be shared freely
- Private Key → must remain secret
ciphertext → [decrypt with private key] → plaintext
📐 Algorithms
- RSA (legacy but still widely used)
- ECC (Curve25519, Ed25519 → modern standard)
⚠️ Trade-off
- slower than symmetric crypto
- not suitable for large data directly
⚙️ Hybrid Encryption (What actually happens)
Real-world systems combine both approaches:
- Generate random session key (symmetric)
- Encrypt data using AES
- Encrypt session key using recipient’s public key
🐧 Installation (Debian)
GnuPG is the reference implementation of OpenPGP.
sudo apt install gnupg
This verifies your crypto backend, supported algorithms and version.
🛠️ GnuPG & Key Storage Internals
GnuPG stores key material in a structured keyring:
| Component | Purpose |
|---|---|
| private-keys-v1.d/ | actual private key blobs (protected) |
| pubring.kbx | public key database (keybox format) |
| trustdb.gpg | trust graph / Web of Trust |
🌍 Exporting Your Public Key
ASCII armor is Base64 + headers, making it safe for transport over text-based systems.
🔍 Fingerprint (Root of Trust)
This is what you verify out-of-band (e.g. in person, Signal, business card).
🔐 Encrypting a Message (Step-by-Step)
📥 Import Recipient Key
✉️ Encrypt File
gpg –encrypt –recipient “email@example.com” message.txt
This produces a hybrid-encrypted file containing:
- encrypted session key
- encrypted payload
- metadata (algorithm, key ID)
📨 Encrypt Inline (ASCII Armor)
Terminate input with CTRL + D
🔓 Decryption
🌐 Publishing Your Key
PGP Public KeyKey ID: 75CA893CEF68BC6B
Fingerprint:
15AD 43D9 20A3 BDBA B2EF
AD59 75CA 893C EF68 BC6B
Download:
https://example.com/publickey.asc
Best practice: host it yourself and optionally mirror to keyservers.
📡 Keyservers & Distribution
gpg –recv-keys KEY_ID
Modern keyservers are append-only → keys cannot truly be deleted.
✍️ Digital Signatures
gpg –verify file.txt.gpg
Signatures provide:
- Integrity → data not modified
- Authenticity → signed by private key holder
- Non-repudiation → cannot deny authorship
🏛️ Trust Models
Centralized (PKI)
- Certificate Authorities (CA)
- used in HTTPS
Decentralized (Web of Trust)
- users sign each other’s keys
- trust is transitive
🧾 Conclusion
- Symmetric → fast, efficient
- Asymmetric → solves identity & key exchange
- Hybrid → real-world standard
- GnuPG → practical implementation of OpenPGP
Cryptography doesn’t eliminate trust — it shifts where you place it.