🌐 Cryptography in Practice
If you use the internet, you are constantly interacting with cryptographic systems—TLS handshakes, package signatures, SSH keys—whether you notice it or not.
💡 Cryptography is not just about secrecy — it’s about authenticity, integrity, and trust distribution in hostile environments.
At its core, modern cryptography is built on two primitives:
- Symmetric encryption (shared secret)
- Asymmetric encryption (public/private key pairs)
🧠 Symmetric Encryption
Symmetric cryptography uses a single secret key for both encryption and decryption. This is computationally efficient and forms the backbone of high-throughput encryption systems.
plaintext → [E_k] → ciphertext
ciphertext → [D_k] → plaintext⚡ Advantages
- O(n) performance with very low overhead
- Hardware acceleration (AES-NI, ARMv8 Crypto Extensions)
- Ideal for bulk data (disks, TLS payloads)
⚠️ Core Problem: Key Distribution
You need a secure channel to exchange the key… which defeats the purpose if you don’t already have one.
🔧 Example
- AES-256 (block cipher, 128-bit block size)
- Modes: GCM (authenticated), CBC (legacy), CTR
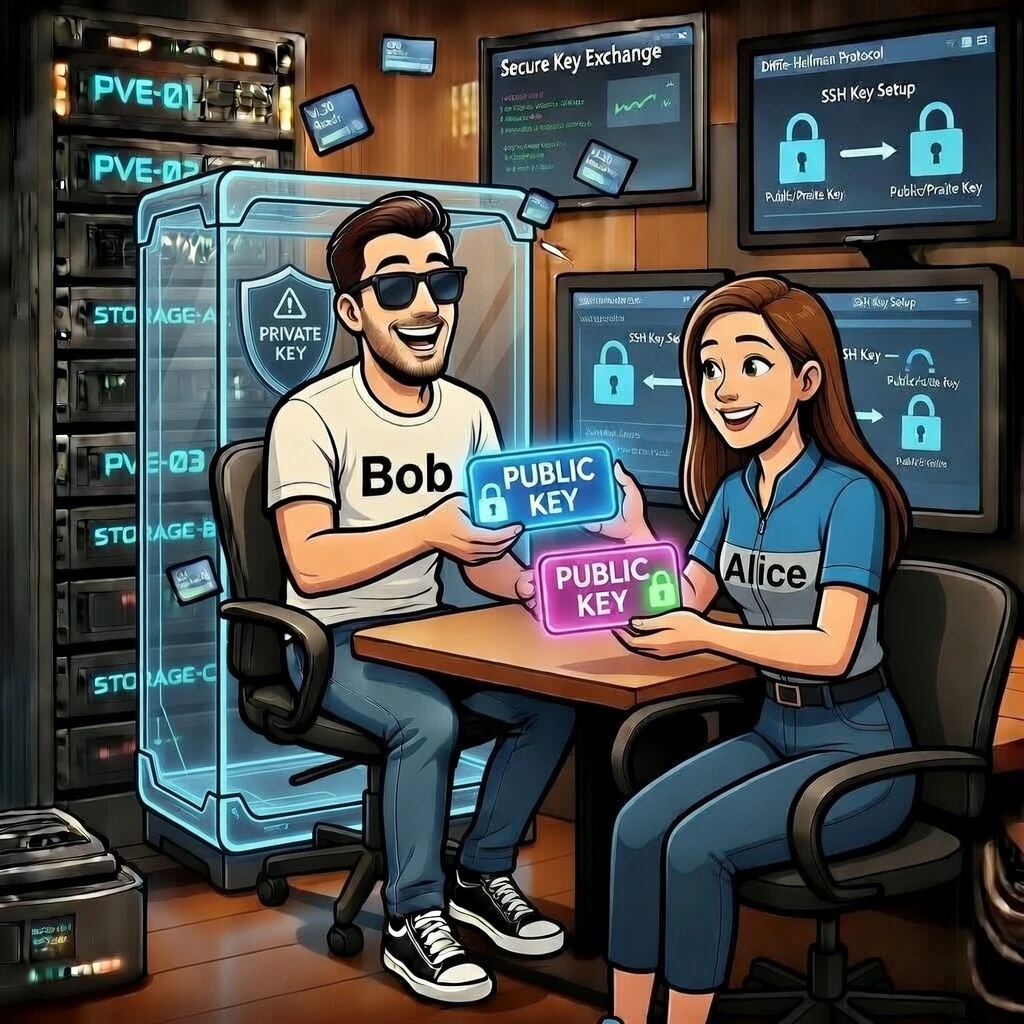
🧬 Asymmetric Encryption
Asymmetric cryptography solves the key distribution problem by splitting identity and secrecy:
- Public Key → can be shared freely
- Private Key → must remain secret
plaintext → [encrypt with public key] → ciphertext
ciphertext → [decrypt with private key] → plaintext🔐 Security is based on hard mathematical problems (e.g. factoring for RSA, discrete logarithms for ECC).
📐 Algorithms
- RSA (legacy but still widely used)
- ECC (Curve25519, Ed25519 → modern standard)
⚠️ Trade-off
- Slower than symmetric crypto
- Not suitable for large data directly
⚙️ Hybrid Encryption (What actually happens)
Real-world systems combine both approaches:
- Generate random session key (symmetric)
- Encrypt data using AES
- Encrypt session key using recipient’s public key
👉 This is exactly how TLS, PGP and modern messaging systems work internally.
🐧 Installation (Debian)
GnuPG is the reference implementation of OpenPGP.
sudo apt update
sudo apt install gnupggpg --versionThis verifies your crypto backend, supported algorithms and version.
🛠️ GnuPG & Key Storage Internals
GnuPG stores key material in a structured keyring:
~/.gnupg| Component | Purpose |
|---|---|
| private-keys-v1.d/ | actual private key blobs (protected) |
| pubring.kbx | public key database (keybox format) |
| trustdb.gpg | trust graph / Web of Trust |
🚨 If your private key is compromised, your entire identity is compromised.
🌍 Exporting Your Public Key
gpg --list-keysgpg --armor --export KEY_ID > publickey.ascASCII armor is Base64 + headers, making it safe for transport over text-based systems.
🔍 Fingerprint (Root of Trust)
gpg --fingerprint👉 The fingerprint is a cryptographic hash of the public key — effectively its immutable identity.
This is what you verify out-of-band (e.g. in person, Signal, business card).
🔐 Encrypting a Message (Step-by-Step)
📥 Import Recipient Key
gpg --import publickey.asc✉️ Encrypt File
echo "Attack at dawn" > message.txt
gpg --encrypt --recipient "email@example.com" message.txtThis produces a hybrid-encrypted file containing:
- Encrypted session key
- Encrypted payload
- Metadata (algorithm, key ID)
📨 Encrypt Inline (ASCII Armor)
gpg --armor --encrypt --recipient "email@example.com"Terminate input with CTRL + D
🔓 Decryption
gpg --decrypt message.txt.gpgNever trust a key without verifying its fingerprint — otherwise you’re vulnerable to MITM attacks.
🌐 Publishing Your Key
PGP Public Key
Key ID: 75CA893CEF68BC6B
Fingerprint:
15AD 43D9 20A3 BDBA B2EF
AD59 75CA 893C EF68 BC6B
Download:
https://example.com/publickey.asc
Best practice: host it yourself and optionally mirror to keyservers.
📡 Keyservers & Distribution
gpg --send-keys KEY_ID
gpg --recv-keys KEY_IDModern keyservers are append-only → keys cannot truly be deleted.
✍️ Digital Signatures
gpg --sign file.txt
gpg --verify file.txt.gpgSignatures provide:
- Integrity → data not modified
- Authenticity → signed by private key holder
- Non-repudiation → cannot deny authorship
🏛️ Trust Models
Centralized (PKI)
- Certificate Authorities (CA)
- Used in HTTPS
Decentralized (Web of Trust)
- Users sign each other’s keys
- Trust is transitive
👉 GPG uses a decentralized trust graph instead of a central authority.
🧾 Conclusion
- Symmetric → fast, efficient
- Asymmetric → solves identity & key exchange
- Hybrid → real-world standard
- GnuPG → practical implementation of OpenPGP
Cryptography doesn’t eliminate trust — it shifts where you place it.
📬 Try It Yourself
I’ve personally worked through all of the examples above to better understand how practical cryptography works in real-world scenarios.
If you’d like to try this yourself, feel free to download my public key from the imprint page:
🔐 I’d be happy to receive an encrypted message from you. I will make sure to reply as quickly as possible — and of course, encrypted as well 😉
This is a great way to test your setup and experience the full workflow of public key cryptography in practice.