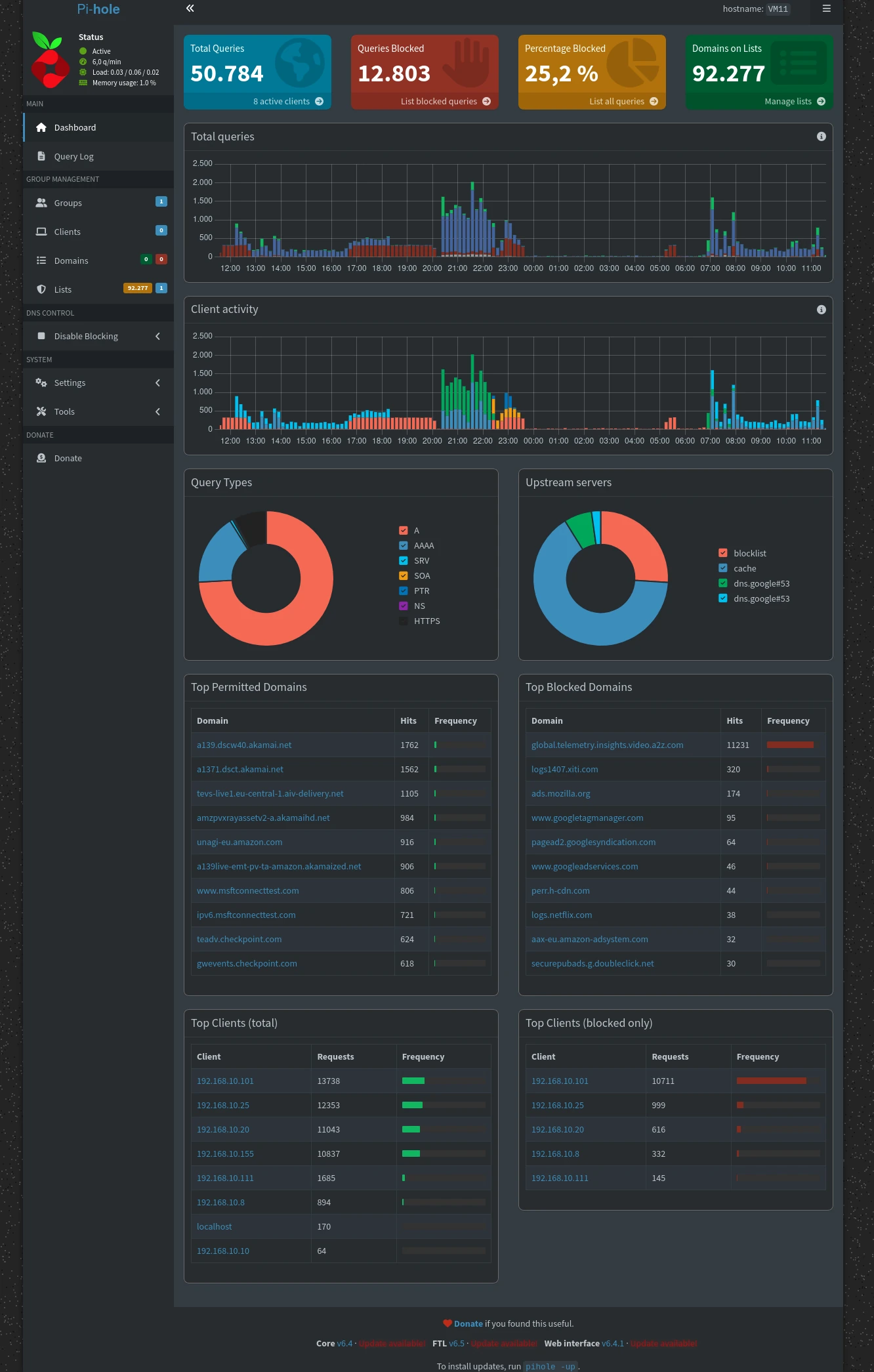
I’m still a big fan of the Pi-hole project.
In my setup, Pi-hole runs 24/7 and basically acts as my personal DNS server. That means it handles all domain name resolution for my network – every single request to the internet passes through it.
Legitimate requests are allowed without any issues, but anything that even remotely looks like advertising, tracking, or shady telemetry gets blocked right away. Think of it as a lightweight, network-wide ad-blocker with a bit of attitude.
I took a look at today’s stats, and it’s pretty impressive: on average, about 25% of all outgoing requests are blocked. That’s a quarter of all traffic – gone.
It’s also funny to see usage patterns. For example, yesterday between 9 PM and 10 PM there was a noticeable spike – clearly some late-night “private computing session” going on 😄
If you’re running any kind of small always-on device at home (a mini server or similar – doesn’t have to be a Raspberry Pi), I can highly recommend setting up Pi-hole. That said, a Raspberry Pi is still a perfect and energy-efficient choice for this kind of job.
There was also a recently disclosed critical security vulnerability in Pi-hole, which is why I updated my installation today. That gave me a good excuse to check the stats again – always nice to see your setup doing its job.
(Screenshot from today’s dashboard attached.)